More from We Live Security

What happens if AI is wrong? – Week in security with Tony Anscombe
Source Cluster:
We Live Security Source Node: 3036011
Time Stamp: Jul 21, 2023

Staying ahead of threats: 5 cybercrime trends to watch
Source Cluster:
We Live Security Source Node: 2980325
Time Stamp: Sep 6, 2023

Trick or treat? Stay so cyber‑safe it’s scary – not just on Halloween
Source Cluster:
We Live Security Source Node: 1733062
Time Stamp: Oct 31, 2022

Crypto mixers: What are they and how are they used?
Source Cluster:
We Live Security Source Node: 1606898
Time Stamp: Jun 20, 2022

Why is my Wi‑Fi slow and how do I make it faster?
Source Cluster:
We Live Security Source Node: 1662879
Time Stamp: Sep 13, 2022

Avoiding data backup failures – Week in security with Tony Anscombe
Source Cluster:
We Live Security Source Node: 2556550
Time Stamp: Mar 31, 2023

DEF CON 31: US DoD urges hackers to go and hack ‘AI’
Source Cluster:
We Live Security Source Node: 2989301
Time Stamp: Aug 18, 2023

Check cybersecurity pre-invest – Week in security with Tony Anscombe
Source Cluster:
We Live Security Source Node: 2989303
Time Stamp: Aug 4, 2023
Top tips for security‑ and privacy‑enhancing holiday gifts
Source Cluster:
We Live Security Source Node: 1771633
Time Stamp: Dec 13, 2022

Black Hat 2022‑ Cyberdefense in a global threats era
Source Cluster:
We Live Security Source Node: 1620252
Time Stamp: Aug 12, 2022
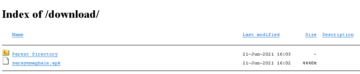
Domestic Kitten campaign spying on Iranian citizens with new FurBall malware
Source Cluster:
We Live Security Source Node: 1727061
Time Stamp: Oct 20, 2022

One login to rule them all: Should you sign in with Google or Facebook on other websites?
Source Cluster:
We Live Security Source Node: 2956175
Time Stamp: Oct 23, 2023
