By کاترین جول، بخش اطلاعات و ارتباطات دیجیتال، WIPO
Today, cybersecurity is a key priority. Staying one-step ahead of the hackers is an increasing challenge as the global cyber threat landscape continues to rapidly evolve. Reports of ransomware attacks are increasingly frequent, crippling business and critical infrastructure (e.g. health, energy, food). The economic fall-out is stunning. According to some estimates the cost of cybercrime is set to rise to USD 10.5 trillion by 2025. Against this backdrop, the Singapore-based company Flexxon, which specializes in next generation hardware cybersecurity and computer memory storage solutions, is on a mission to safeguard the interests of digital citizens. مجله WIPO recently met with Flexxon’s CEO and co-founder, Camellia (Cam) Chan, to learn more about the company’s novel approach to cybersecurity and its commitment to innovation and IP. Flexxon is a winner of the 2023 WIPO Global Awards.
Our mission is to change the way people think about data protection and to offer digital citizens a greater sense of security in the cyber world.

What prompted you to set up Flexxon?
I worked for some years in big companies in Asia and learned many useful skills. But I have always been passionate about innovation and knew that I needed to follow my dream of creating something that could really make an impact in the world.
So in 2007, my co- founder May Chng and I, started فلکسون, using our expertise to make products that solve the practical problems our customers face and to build a company that is all about innovation, openness, and fairness.
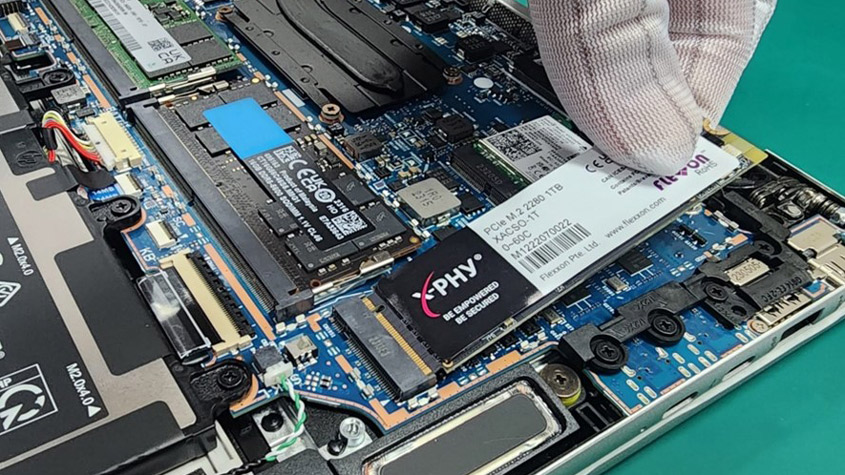
Fast forward 15 years, we have gone global, we have multiplied our team more than 20-fold and we have ventured into the critically important cybersecurity industry. In 2021, we launched our X-PHY AI Cybersecure SSD, the world’s first AI embedded firmware-based cybersecurity solution. X-PHY® is capable of detecting data access anomalies and shutting down potential ransomware attacks in real-time without human intervention. It is a last line of defense against evolving cyber threats at the hardware level.
What is Flexxon’s mission?
Our mission is to change the way people think about data protection and to offer digital citizens a greater sense of security in the cyber world by developing the most innovative, secure, effective, and advanced cybersecurity data storage solutions.
Who are Flexxon’s customers and what services do you offer?
Our flagship AI cybersecurity solution is available in 20 countries, providing businesses with new levels of protection against evolving cyber threats. Primarily, we serve customers in the industrial, medical, automotive, and military sectors, including Fortune 500 companies like ABB, Bosch Schneider, Honeywell and Johnson and Johnson.
X-PHY® offers our customers a new level of protection against cyber threats. The technology cycle in cybersecurity moves fast, so we help our clients prolong the longevity of their memory storage technology, ensuring it remains compatible with prevailing market solutions.
How would you characterize the problem of cyber security and the impact of cybercrime?
مشاغل امنیتی سایبری estimates that by 2025, the cost of cybercrime will reach USD 10.5 trillion. Our solution will help reduce that, but cybercrime is not going away.
When your network goes down because of cybercrime, it’s disruptive, but you call your service provider, and it gets fixed. But if your data is compromised, through ransomware, that’s painful. Even if you pay, you may not get your data back. And you also suffer reputational damage and fines.
In ransomware attacks, cyber criminals infiltrate your network, and without you even noticing, they clone your data and sell it in the dark web.
In ransomware attacks, cyber criminals infiltrate your network, and without you even noticing, they clone your data and sell it in the dark web. Then you discover there’s been a data breach – sometimes, this can take years to detect. Ransomware attacks are becoming increasingly frequent and make up the largest share of cybercrime. That’s why it’s so important to protect data. We can’t take care of everything, but we take care of data, which is critical.
Now, we’re facing even bigger challenges. Cyberattacks are being weaponized. Large-scale industrial and essential services rely heavily on digital systems, and a cyberattack can result in losing control of critical equipment and warning systems. Take for example, the fall-out from حمله باج افزار استعماری Pipeline in 2021, the largest cyberattack on an oil infrastructure target in the USA.
We have a new solution in the pipeline to safeguard against such events. Our patent for that solution was just granted in Singapore, and we’re now extending protection to other key markets. It will launch in early 2024. An expanded version of X-PHY, it will monitor activities in all memory chipset media. All activities leave a trace inside the memory, so as long as we monitor the entire memory, we will be safe.
The cybersecurity landscape is increasingly challenging.
The cybersecurity landscape is increasingly challenging. At present, the world relies heavily on static solutions, like encryption, firewalls, antivirus software and key management, to protect hardware. These solutions had no “intelligence” or in-built controller, to detect threats in real-time. That makes them vulnerable to hacking. By leveraging AI technology and embedding it into our memory storage systems, we give memory storage the ability to manage the data independently and to protect it from cyberattacks. Our solution is hardware based. We use existing AI algorithms because hardware never really changes, so you don’t need a sophisticated AI system for this purpose.
Is Flexxon’s technology the ultimate silver bullet against cybercrime?
No, currently we are only protecting the valuable data that sits in hardware. We are one form of defense in a much larger battlefield. We cannot protect against social engineering or other types of fraud. That’s why users still need to maintain cyber hygiene and to be very wary of what they click on.
Why do approaches to cybersecurity need to change?
For the last 30 years, the cybersecurity market has focused on software-based solutions. But this approach covers only six of the seven layers of OSI network architecture, which supports the interoperability of products and software. They neglect the physical level – the hardware – where the most valuable data is stored.

The focus on software solutions has encouraged a reactive approach, requiring constant updating and monitoring. It also makes users responsible for maintaining cybersecurity and monitoring threats, like phishing attacks. Yet, cyberattacks are on the rise. As an example of the scale of the problem, in 2021, Microsoft reported over 600 billion monthly security events, of which only 500 were remedied. Humans are the cause of 95 percent of data breaches. Exploiting human error is one of the most successful tactics used by cybercriminals. It takes just one click on a malicious link for a hacker to gain access.
The conventional wisdom is people, process, and technology. But in the current cyber threat landscape this approach is no longer sufficient.
The conventional wisdom is people, process, and technology. But in the current cyber threat landscape this approach is no longer sufficient. We need a proactive approach, and we need complementary solutions that add another layer of protection. By securely protecting memory storage – this is where everything, from your system activities to your user data, is stored – it’s easier to monitor data and defend against cyberattacks.
That’s why our X-PHY technology focuses on the physical layer and deploys AI in an enclave environment. Instead of monitoring millions of possibilities, it looks for specific “read and write” patterns that attempt to gain access to data autonomously and in real-time. With X-PHY, it is possible to identify bad actors immediately, lock down the device, and protect users’ data. Our simplified solution is the only one of its kind so far. We believe it is the way forward for cybersecurity.
By protecting memory storage, you have a last line of defense if all else fails.
But this approach challenges conventional wisdom and the market that has developed around it. So, there’s a lot of resistance. But our solution simply adds a complementary new safety mechanism to protect data at the core memory storage level. We’re simply back-stopping cybersecurity software solutions. By protecting memory storage, you have a last line of defense if all else fails.
Would you like to see more regulation to crack down on cybercrime?
Yes and no. Unfortunately, you can’t regulate the hacker. But if we adopt a business-as-usual approach, we’re not addressing 95 percent of the problem. Regulation is always a double-edged sword. More regulation means less creativity. We need regulation, but it needs to be balanced and sensitive to the need for creativity.
Unfortunately, you can’t regulate the hacker. But if we adopt a business-as-usual approach, we’re not addressing 95 percent of the problem.
How is Flexxon promoting the uptake of its cybersecurity technology around the world?
We are partnering with major PC manufacturers, such as ASUS, Dell, HP, and Lenovo. That allows Flexxon to integrate our multi-patented innovation into well-known and respected products. In time, we also plan to start licensing our technology to competitors, so they embed it in their solid state drives (SSDs).
How would you like to see the cybersecurity landscape evolve?
We are here to ensure the cybersecurity of all digital citizens. Once our technology is part of the collaborative ecosystem, the cyber landscape will become a more secure environment. The recognition our IP has received is testimony to its game-changing nature.
IP is part of our corporate DNA. At Flexxon, we are laser-focused on innovation. We invest heavily in R&D to speed up product development and we recognize the importance of safeguarding our hard work and investment in each breakthrough solution. We currently have 30 patents and 27 trademarks granted globally over the last three years. And we’re leveraging our extensive IP portfolio to gain a strategic advantage in the market, increase our brand recognition, protect our innovations, and generate future licensing and partnership opportunities in both B2B and the B2C markets.
IP is part of our corporate DNA. At Flexxon, we are laser-focused on innovation.
The focus of our 80-strong team is how to create value and how to grow the company. IP is central to our ability to scale up our operations and grow. It enables us to maintain our competitive advantage and is supporting our ambition for them to become a de facto industry standard.
Tell us about Flexxon’s IP strategy.
Flexxon has a comprehensive international strategy to protect and enforce our IP rights in key markets. This enables us to maintain our competitive edge, build credibility with customers, partners, and investors, and ensure sustained global growth.
IP is central to our ability to scale up our operations and grow.
Our management team is committed to fostering a culture of creativity and innovation within the company, for example, by recognizing and rewarding employees who contribute to the development of our IP. We also work with IP specialists to enhance our IP management capabilities.
Who produces X-PHY® and Flexxon’s other memory storage solutions?
We develop and design everything from scratch and we outsource production to our manufacturing partners in Singapore. We have strict non-disclosure agreements (NDAs) in place with them for that.
What are Flexxon’s key current challenges?
While we see every problem as an opportunity, changing the mindset of the cybersecurity industry and its firm adherence to software solutions is a big challenge, even in the face of increasing vulnerability to cyberattacks. So, we need to build greater understanding about how our technology complements conventional approaches.
What does it mean for you to be a winner of the WIPO Global Award and how is it going to help your business?
The recognition that we have received from the جایزه will help us continue to grow, innovate, and contribute positively to the cybersecurity landscape. It will also give more people the confidence to test and adopt our technology. The Award will be very helpful in opening up all kinds of ways of making the impossible possible, and of course, will help attract the investment we need to scale.
Our journey demonstrates that IP is not just for the big boys with deep pockets and large IP teams.
With this Award, we aim to demonstrate to other SMEs that even a small player in a vast market can make a difference when they leverage on their deep tech and IP to foster growth. Our journey demonstrates that IP is not just for the big boys with deep pockets and large IP teams. SMEs can also build up their IP portfolio, level the playing field, and compete on equal terms. If Flexxon can do it, others can too!

برنامه های شما برای آینده چیست؟
We will continue to work with our global partners to reinforce the message about the need for a proactive approach to cybersecurity measures to build a safer and more secure digital world.
- محتوای مبتنی بر SEO و توزیع روابط عمومی. امروز تقویت شوید.
- PlatoData.Network Vertical Generative Ai. به خودت قدرت بده دسترسی به اینجا.
- PlatoAiStream. هوش وب 3 دانش تقویت شده دسترسی به اینجا.
- PlatoESG. کربن ، CleanTech، انرژی، محیط، خورشیدی، مدیریت پسماند دسترسی به اینجا.
- PlatoHealth. هوش بیوتکنولوژی و آزمایشات بالینی. دسترسی به اینجا.
- منبع: https://www.wipo.int/wipo_magazine/en/2023/04/article_0008.html
- : دارد
- :است
- :نه
- :جایی که
- $UP
- 1
- 10
- سال 15
- ٪۱۰۰
- 20
- 2021
- 2023
- 2024
- 2025
- 27
- 30
- 500
- 600
- 8
- 9
- a
- توانایی
- درباره ما
- بالاتر
- دسترسی
- دسترسی به داده ها
- مطابق
- فعالیت ها
- بازیگران
- اضافه کردن
- خطاب به
- می افزاید:
- تبعیت
- اتخاذ
- پیشرفته
- مزیت - فایده - سود - منفعت
- طرفداران
- در برابر
- موافقت نامه
- پیش
- AI
- هدف
- الگوریتم
- معرفی
- اجازه می دهد تا
- همچنین
- همیشه
- هدف - آرزو
- an
- و
- دیگر
- آنتی ویروس
- آنتی ویروس نرم افزار
- روش
- رویکردها
- معماری
- هستند
- دور و بر
- AS
- آسیا
- اسوس
- At
- حمله
- کوشش
- جذب
- خودرو
- بصورت خودگردان
- در دسترس
- جایزه
- جوایز
- دور
- B2B
- B2C
- به عقب
- پس زمینه
- بد
- متعادل
- مستقر
- میدان جنگ
- BE
- زیرا
- شدن
- تبدیل شدن به
- بوده
- بودن
- باور
- بزرگ
- بزرگتر
- بوش
- هر دو
- جعبه
- نام تجاری
- شناخت برند
- شکاف
- نقض
- دستیابی به موفقیت
- ساختن
- کسب و کار
- کسب و کار
- اما
- by
- صدا
- CAN
- نمی توان
- قابلیت های
- توانا
- اهميت دادن
- علت
- مرکزی
- مدیر عامل شرکت
- به چالش
- چالش ها
- به چالش کشیدن
- چان
- تغییر دادن
- تبادل
- متغیر
- مشخص کردن
- چیپ ست
- شهروندان
- کلیک
- مشتریان
- بنیانگذاران
- بنیانگذاران
- مشترک
- تعهد
- مرتکب شده
- شرکت
- شرکت
- شرکت
- سازگار
- رقابت
- رقابتی
- رقبای
- مکمل
- جامع
- در معرض خطر
- کامپیوتر
- اعتماد به نفس
- ثابت
- ادامه دادن
- ادامه
- کمک
- کنترل
- کنترل کننده
- معمولی
- هسته
- شرکت
- هزینه
- میتوانست
- کشور
- دوره
- را پوشش می دهد
- ترک
- ایجاد
- ایجاد ارزش
- ایجاد
- خلاقیت
- اعتبار
- جنایتکاران
- فلج کننده
- بحرانی
- زیرساخت های بحرانی
- فرهنگ
- جاری
- در حال حاضر
- مشتریان
- سایبر
- امنیت سایبری
- حمله سایبری
- حملات سایبری
- جرایم اینترنتی
- مجرمان سایبری
- امنیت سایبری
- نرم افزار امنیت سایبری
- چرخه
- خسارت
- تاریک
- وب سایت تیره
- داده ها
- دسترسی به داده ها
- نقض داده ها
- خرابی داده ها
- حفاظت از داده ها
- ذخیره سازی داده ها
- de
- عمیق
- فناوری عمیق
- دفاع
- دره کوچک و تنگ
- نشان دادن
- نشان می دهد
- مستقر می کند
- طرح
- تشخیص
- توسعه
- توسعه
- در حال توسعه
- پروژه
- دستگاه
- تفاوت
- دیجیتال
- دنیای دیجیتال
- كشف كردن
- نفاق افکن
- بخش
- DNA
- do
- میکند
- آیا
- پایین
- رویا
- درایو
- e
- هر
- در اوایل
- آسان تر
- اقتصادی
- اکوسیستم
- لبه
- موثر
- دیگر
- جاسازی کردن
- جاسازی شده
- تعبیه کردن
- کارکنان
- را قادر می سازد
- تحت محاصره
- تشویق
- رمزگذاری
- انرژی
- اعمال
- مهندسی
- بالا بردن
- اطمینان حاصل شود
- حصول اطمینان از
- تمام
- محیط
- برابر
- تجهیزات
- خطا
- ضروری است
- خدمات ضروری
- تخمین می زند
- اتر (ETH)
- حتی
- حوادث
- هر
- همه چیز
- تکامل یابد
- در حال تحول
- مثال
- موجود
- منبسط
- تخصص
- گسترش
- وسیع
- چهره
- نما
- نتواند
- عدالت
- بسیار
- FAST
- رشته
- جریمه
- فایروال ها
- شرکت
- نام خانوادگی
- ثابت
- کشتی دریادار
- تمرکز
- متمرکز شده است
- تمرکز
- به دنبال
- غذا
- برای
- فرم
- ثروت
- به جلو
- پرورش دادن
- پرورش دادن
- موسس
- تقلب
- مکرر
- از جانب
- آینده
- افزایش
- تولید می کنند
- نسل
- دریافت کنید
- دادن
- جهانی
- در سطح جهانی
- می رود
- رفتن
- رفته
- اعطا شده
- بیشتر
- شدن
- رشد
- هکر
- هکرها
- هک
- بود
- سخت
- کار سخت
- سخت افزار
- آیا
- سلامتی
- به شدت
- کمک
- مفید
- اینجا کلیک نمایید
- شرکت Honeywell
- چگونه
- چگونه
- HP
- HTML
- HTTPS
- انسان
- انسان
- i
- شناسایی
- if
- تصاویر
- بلافاصله
- تأثیر
- اهمیت
- مهم
- غیر ممکن
- in
- از جمله
- افزایش
- افزایش
- به طور فزاینده
- به طور مستقل
- صنعتی
- صنعت
- اطلاعات
- شالوده
- نوآوری
- ابداع
- نوآوری
- ابتکاری
- داخل
- در عوض
- ادغام
- اطلاعات
- منافع
- بین المللی
- قابلیت همکاری
- مداخله
- به
- سرمایه گذاری
- سرمایه گذاری
- سرمایه گذاران
- IP
- IT
- ITS
- جانسون
- سفر
- JPG
- تنها
- فقط یکی
- کلید
- نوع
- چشم انداز
- لپ تاپ
- بزرگ
- در مقیاس بزرگ
- بزرگتر
- بزرگترین
- نام
- راه اندازی
- راه اندازی
- لایه
- لایه
- رهبری
- یاد گرفتن
- آموخته
- ترک کردن
- ترک کرد
- خیر
- کمتر
- سطح
- سطح
- قدرت نفوذ
- بهره برداری
- صدور مجوز
- پسندیدن
- لاین
- ارتباط دادن
- قفل
- طولانی
- دیگر
- طول عمر
- مطالب
- شکست
- خیلی
- حفظ
- نگهداری
- عمده
- ساخت
- باعث می شود
- ساخت
- مخرب
- مدیریت
- مدیریت
- تیم مدیریت
- تولید کنندگان
- تولید
- بسیاری
- بازار
- بازارها
- ممکن است..
- متوسط
- به معنی
- معیارهای
- مکانیزم
- رسانه ها
- پزشکی
- حافظه
- پیام
- با
- مایکروسافت
- نظامی
- میلیون ها نفر
- ذهنیت
- ماموریت
- مانیتور
- نظارت بر
- ماهیانه
- بیش
- اکثر
- حرکت می کند
- بسیار
- ضرب
- my
- طبیعت
- نیاز
- ضروری
- نیازهای
- شبکه
- هرگز
- جدید
- راه حل جدید
- بعد
- نه
- رمان
- اکنون
- of
- ارائه
- پیشنهادات
- نفت
- on
- یک بار
- ONE
- فقط
- افتتاح
- باز بودن
- عملیات
- فرصت ها
- فرصت
- or
- دیگر
- دیگران
- ما
- توسعه
- برون سپاری
- روی
- دردناک
- بخش
- همکاری
- شرکای
- همکاری
- احساساتی
- حق ثبت اختراع
- اختراعات
- الگوهای
- پرداخت
- PC
- مردم
- در صد
- فیشینگ
- حملات فیشینگ
- عکس
- فیزیکی
- خط لوله
- محل
- برنامه
- برنامه
- افلاطون
- هوش داده افلاطون
- PlatoData
- بازیکن
- بازی
- به علاوه
- جیب
- مقام
- مثبت
- فرصت
- ممکن
- پتانسیل
- عملی
- در حال حاضر
- در درجه اول
- اولویت
- بلادرنگ
- مشکل
- مشکلات
- روند
- تولید می کند
- محصول
- توسعه محصول
- تولید
- محصولات
- وعده
- ترویج
- محافظت از
- حفاظت
- حفاظت
- محافظت می کند
- ارائه دهنده
- ارائه
- هدف
- تحقیق و توسعه
- باجافزار
- حملات باج افزار
- سریعا
- RE
- رسیدن به
- زمان واقعی
- واقعا
- اخذ شده
- تازه
- به رسمیت شناختن
- شناختن
- شناختن
- كاهش دادن
- تنظیم کردن
- تنظیم
- تقویت کردن
- تکیه
- بقایای
- گزارش ها
- مقاومت
- احترام
- مسئوليت
- نتیجه
- پاداش
- راست
- حقوق
- طلوع
- s
- امن
- حفاظت
- امن تر
- ایمنی
- می گوید:
- مقیاس
- خراش
- ثانوی
- بخش ها
- امن
- ایمن
- تیم امنیت لاتاری
- رویدادهای امنیتی
- دیدن
- فروش
- حس
- حساس
- خدمت
- سرویس
- ارائه دهنده خدمات
- خدمات
- تنظیم
- هفت
- اشتراک گذاری
- نقره
- ساده شده
- به سادگی
- سنگاپور
- نشسته است
- شش
- مهارت ها
- کوچک
- شرکتهای کوچک و متوسط
- So
- تا حالا
- آگاهی
- مهندسی اجتماعی
- نرم افزار
- جامد
- راه حل
- مزایا
- حل
- برخی از
- چیزی
- گاهی
- مصنوعی
- متخصصان
- تخصص دارد
- خاص
- سرعت
- استاندارد
- شروع
- آغاز شده
- دولت
- اقامت
- هنوز
- ذخیره سازی
- ذخیره شده
- استراتژیک
- استراتژی
- سخت
- خیره کننده
- موفق
- چنین
- کافی
- حمایت از
- پشتیبانی از
- پایدار
- شمشیر
- سیستم
- سیستم های
- T
- برخورد با
- تاکتیک
- گرفتن
- طول می کشد
- هدف
- تیم
- تیم ها
- فن آوری
- پیشرفته
- قوانین و مقررات
- آزمون
- شهادت
- نسبت به
- که
- La
- آینده
- جهان
- شان
- آنها
- سپس
- اینها
- آنها
- فکر می کنم
- این
- تهدید
- تهدید
- سه
- از طریق
- زمان
- عنوان
- به
- بالا
- رد
- علائم تجاری
- تریلیون
- انواع
- نهایی
- درک
- متاسفانه
- به روز رسانی
- جذب
- us
- ایالات متحده
- دلار آمریکا
- استفاده کنید
- استفاده
- مفید
- کاربر
- کاربران
- با استفاده از
- ارزشمند
- ارزش
- وسیع
- نسخه
- بسیار
- آسیب پذیری
- آسیب پذیر
- هشدار
- بود
- مسیر..
- راه
- we
- ما یکی هستیم
- وب
- معروف
- بود
- چی
- چه زمانی
- که
- WHO
- چرا
- ویکیپدیا
- اراده
- برنده
- خرد
- با
- در داخل
- بدون
- مهاجرت کاری
- مشغول به کار
- جهان
- جهان
- خواهد بود
- سال
- هنوز
- شما
- شما
- زفیرنت