We can distinguish two prevalent types of wallets: software and hardware wallets. They fulfill the same function, but in a different way. Software wallets are considered simpler to use: a single program is enough to create, validate and sign transactions. With a software wallet, it is not necessary to create the transaction on the software and confirm it on a hardware device.
دو ہفتے پہلے، حرام کہانیاں unveiled a targeted attack against thousands of people around the world. This attack exploited vulnerabilities on Android and iOS, to install spyware developed by the NSO Group: Pegasus. This malware is able to monitor the whole activity of the device, and to exfiltrate personal information: SMS, WhatsApp and Signal conversations, phone calls, etc. This article explains how, under these conditions, such a malware would be able to extract all the secrets of a software wallets, and the differences from a security point of view between software wallets on mobile phones and desktop computers.
This article is intended to be not very technical. To keep it relatively simple, only basic features will be discussed.
Protecting secrets
What is stored in a crypto wallet?
Wallets do not actually store the users’ cryptocurrencies: they only store the secrets, notably the private keys, that allow to access the cryptocurrencies and the ability to spend them. These private keys are mostly ECC (elliptic curve cryptography) private keys on different curves depending on the blockchain. The most common curves are secp256k1 (Bitcoin, Ethereum…), Ed25519 (Monero), or BLS12-381 (Ethereum 2).
These keys are used to sign transactions, and more generally to interact with blockchain assets.
The storage of these keys depends on the type of wallet: deterministic or not. A Hierarchical Deterministic (HD) wallet allows the creation of a tree of keys from a single master secret called the seed (cf BIP44). This seed is often derived from a mnemonic sequence of 12, 18 or 24 words randomly generated or chosen by the user (cf.BIP39). These mnemonics allow to limit the number of keys to be stored: they can be recomputed anytime from the seed. HD wallets only store this mnemonic or the seed.
Non deterministic wallets generate a new key for each use and must store all of them. Non-deterministic wallets can’t be easily migrated to another wallet since backups are not compatible.
The main security features of a wallet consist in generating, storing and using these secrets properly. There are different levels of security against different types of threats:
- Protection against “evil maid” attacks : An attacker with temporary access to the wallet mustn’t be able to add a backdoor inside the wallet allowing to steal the PIN or the password protecting secrets.
- Secure cryptographic material : Keys and nonce generated by the wallet must never be predictable. Furthermore the knowledge of secrets (except the seed) generated at some point in time shall not allow to predict the secret to be generated in the future.
- Protection at rest : If an attacker obtains persistent data of a software wallet, they must not be able to extract the keys.
- Protection during secret use: When the wallet is unlocked, the keys must not be accessible by an attacker or a malware.
ہارڈویئر بٹوے
The security model of a hardware wallet aims at obviating these security threats. Hardware wallets protect against malware by design. They are independent devices which sign transactions on their own. The cryptographic materials always stay inside the device and are never sent to the software application to which they communicate. The communication interface is always simple which drastically reduces the attack surface. It can be USB, Micro SD or camera + screen (through QR code), or Bluetooth Low Energy.
Furthermore, hardware wallets embed a screen directly into the device allowing the user to verify the actions he’s about to do when he interacts with his secret keys. These manual checks on devices are a very efficient countermeasure against malware on the computer/mobile. Where malware on a computer/mobile device could access the secrets (seed or private keys) or even swap/modify addresses or amounts when the user is performing a transaction, this is not possible with a hardware wallet.
Hardware wallets are also designed to protect against “evil maid” attacks and against an attacker with physical access. Depending on the hardware wallet, they have different levels of security, but in all cases they are designed to secure against these threats. A detailed description of Ledger Nano threat models can be found یہاں.
سافٹ ویئر والیٹس
Regular software wallets protect secrets with regular means: security mechanisms of the operating system on which they run and sometimes an access control based on a PIN or a password.
In the following, desktop (Windows, macOS, Linux) wallets and mobile wallets are considered. The main differences between them mostly rely on the security mechanisms offered by the operating system.
Software wallets on a computer
Several popular wallets, such as Electrum, Exodus, Atomic or Bitcoin core, run on computers.
On a computer, security mechanisms offered by the operating system to isolate a wallet process from other processes are limited. Most apps are run by the same user, and apps are allowed to read other application’s data.
The security of these software wallets mainly relies on the security of the password that protects them, and also on the fact that no malware runs on the OS (which is quite difficult to guarantee, see recent news regarding Pegasus).
Most of the time, the seed is stored in an encrypted container protected by a password.A straightforward attack consists, for a malware or a remote administration tool, to retrieve this encrypted container and send it to the attacker. Then the password can either be brute-forced or obtained through using a keylogger کے.
In a scenario where an attacker only manages to access the encrypted container (the attacker finds a USB key containing a wallet, or installs malware on a computer, but the victim never opens his wallet application), the attacker has to brute force the password.
Most passwords are بری. There are billions of passwords that leaked on the web, and many people tend to reuse their passwords for several services. Ready-made tools allow you to retrieve passwords for cryptocurrencies wallets, such as btcrecover or ہیشکیٹ. Passwords can be complex, but behind each wallet there is real money, hence attackers won’t hesitate to invest resources to break such passwords.
Two basic security principles to keep your passwords secure are to use a password manager, and to never reuse your password for different purposes.
The most concerning threat for software wallets are dedicated malware and stealers, developed specifically to drain your funds. Such malware, such as KPOT or الیکٹروٹریٹ, do not even have to bruteforce your password: they can directly capture it when you enter it, decrypt the wallet configuration data, and exfiltrate the seed.
Here is a toy application, developed for this article, that targets the Electrum wallet (though it could have been another software wallet). It simulates a malware that steals the user password when it is entered by the victim. Password is then used to decrypt the wallet data, and to display the seed:
As you see, even if the password is complex, the app is able to retrieve it as it directly sniffes it in memory.
This example is very similar to the recent .SCR malware campaigns used to steal cryptocurrencies. Criminals used social engineering techniques to trick users into downloading a malicious screensaver. This screensaver was actually stealing information from the computer’s victim, including wallet and cryptocurrency exchange information.
To conclude on software wallets running on computers:
- In most cases software wallets running on computers protect the user’s seed using a password.
- The access control for these wallet files mainly rely on the security of the computer. In practice, it is hard to protect computers from malware, and as cryptocurrencies become mainstream, attacks against wallets will become more and more sophisticated.
- Using such software wallets to secure digital assets is not a good idea. Any specialized malware will be able to get the wallet files and find the passwords offline, or get the password through a keylogger.

Software wallets on a smartphone
Android and iOS smartphones offer by default security features that are not widely used on desktop operating systems.
Mobile operating systems offer app and user data protection. In particular, app sandboxes are mandatory for all apps. This is not the case on, for instance, Windows: by default, any application can access user data.
Hence, a malicious app cannot read data from another app, except if:
- It finds a vulnerability on that app.
- Or it manages to escalate privileges, for example by exploiting a kernel vulnerability allowing it to gain root access to the system.
Unfortunately, such attacks exist. They are much easier on outdated versions of Android and iOS, and on older or cheap devices where third-party code is often less secure.
On an up-to-date OS, these attacks are harder but not remotely unfeasible. For example, Ian Beer showed an extremely impressive zero-click attack on iOS 13.5 in December 2020. Guang Gong presented an exploit chain to remotely root a wide range of Qualcomm-based Android devices in June 2020. And, two weeks ago, حرام کہانیاں unveiled that NSO Group used an exploit chain to target recent iOS and Android devices using 0-day vulnerabilities.
Less sophisticated attackers can use local vulnerabilities allowing them to extract wallet data from a malicious application. Vulnerability brokers such as Zerodium pay اپ 200,000 ڈالر for a privilege escalation to root on Android and iOS, but up to $1,500,000 for remote attacks.
We studied a couple of Android/iOS wallets. Their security depends on the app itself, but also on the security features of the underlying OS. Of course, when the security of the operating system is defeated, the application is not secure anymore
Two methods to protect the seed are commonly used:
- پاس ورڈ کی حفاظت – wallet data is protected by a password entered by the user. The design is the same as for desktop wallets. In practice, data is harder to extract than from a computer, as retrieving app data from a malicious app is technically more difficult, for the reasons explained above. However, retrieving the password once the data has been stolen is in practice easier: entering complex passwords on mobile phones is tedious, hence users tend to choose simpler ones. Moreover, key derivation mechanisms (used to create a key from a password) on mobile devices are usually simpler to break, as they are often more lightweight for performance reasons.

- سکےومی and Metamask are examples of such wallets.
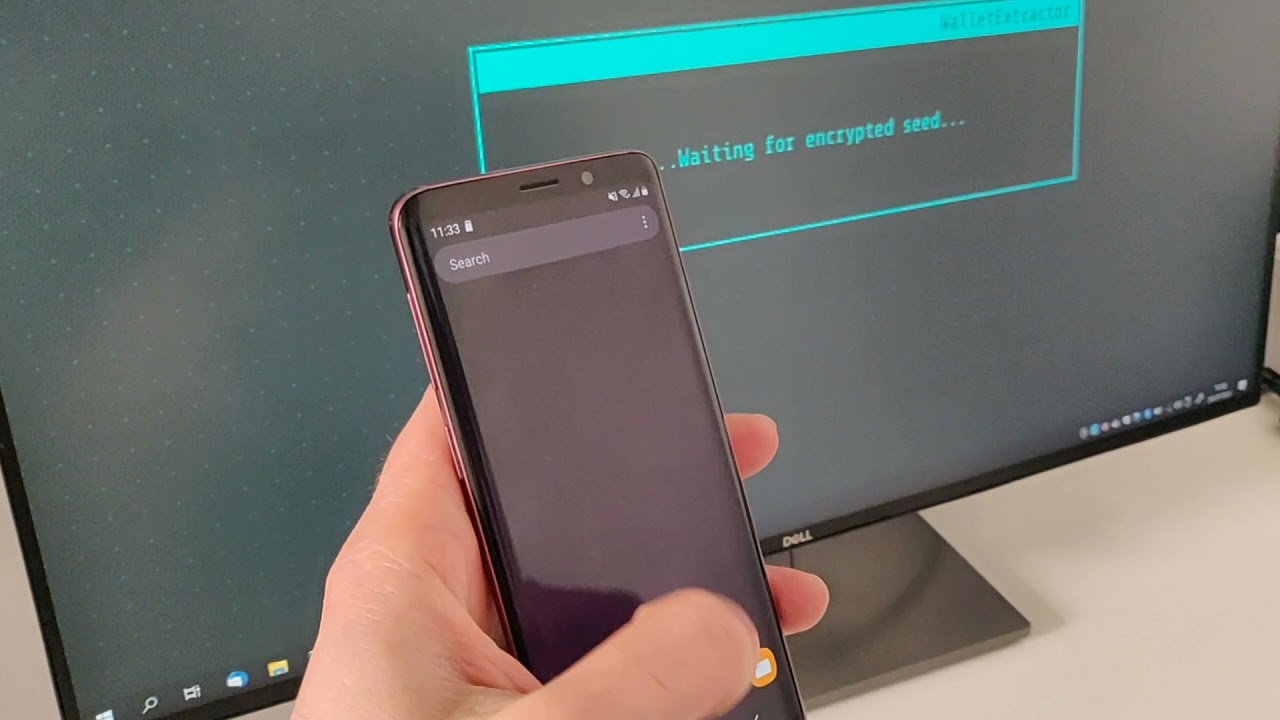
In the following video, we show another toy app developed for this article. It is a malware disguised as a fake Bitcoin ticker widget. Malware exploits a known vulnerability on an unpatched device to get a root acess on the device, and to exfiltrate the encrypted seed to a remote server. The server then bruteforces the password to decrypt the seed.
This method is not specific to a wallet. It can be (more or less) easily adapted to any password protected wallet. Here is he same example with Coinbase Wallet:
[سرایت مواد]
- Security based on the Android Keystore (or iOS Keychain) – In this case, wallet data is encrypted with an encryption key stored in the Android Keystore (iOS Keychain). These services were initially designed to securely store encryption keys, and many apps use them to generate a key that will encrypt all the sensitive user data.Applications using the Keystore implement the following mechanism:
- The app asks the Keystore to generate an encryption key for a given identifier. Keystore generates the key and stores it securely.
- When the app wants to encrypt or decrypt a blob, it sends the blob along with the key identifier to the Keystore.
- Finally, the keystore checks if the app has actually the rights to use this key and sends back then output data to the app.
With this model, the app can’t know the value of the key but can use it. It is also possible to associate additional access controls to the key: for example, key access can be conditioned to a user authentication (request for a PIN or unlock pattern).
This mechanism can provide additional security, compared to password based protection. Indeed, on recent phones, the Keystore is backed by a Trusted Execution Environment (TEE), or sometimes a Secure Element.

That means an attacker with root privileges won’t be able to extract encryption keys from the keystore. Nevertheless, they will be able to use the Keystore as a decryption oracle, and to encrypt or decrypt any data they want.

Keystore offers encryption, but also signing services. So, could a wallet protect its encryption keys, making them difficult to extract? The answer is unfortunately no: software wallets do not use Keystore to sign transactions، اور private keys are always manipulated in plaintext by the app.
This is for a simple reason: KeyStore and KeyChain offer generic signature and encryption services, but don’t support the cryptography used in cryptocurrencies. For instance, the KeyStore implements ECDSA Signature but only on NIST curves defined in FIPS 186-4 (P-224, P-256, P-384 and P-521). Bitcoin uses another curve, secp256k1, which is not supported yet.
To summarize, Keystore and Keychain are good services to protect secret and private keys. They can offer some security by encrypting sensitive data: some classes of vulnerabilities (arbitrary file read, for example) will be tacked by Keystore encryption. However, if a root privilege escalation is not enough to extract the key values from a hardware-backed Keystore, it is sufficient to decrypt sensitive data. An attacker able to instrument the app is able to retrieve its secrets.
To conclude on mobile wallets:
- The isolation mechanism between apps provided by iOS/Android raises the bar for security compared to a software wallet running on a computer. The attacker needs first a privilege escalation to access app data. This is feasible on outdated devices. Skilled attackers (Ian Beer did it in 6 months alone but… It is Ian Beer) can also do it on recent, patched devices.
- Key protection services (KeyStore, KeyChain) could add an additional layer of security for protecting secrets at rest. Nevertheless, as they don’t support cryptographic algorithms for cryptocurrency applications, key can still be extracted.
- In all cases, an attacker with a root access can either retrieve the seed at rest, when used, or leverage the user’s rights to empty the wallet using the software wallet as an oracle.
Here is a last example of a toy spyware targetting the Blockchain.com wallet (though this could be performed on many other wallets just as easily). It is installed remotely, and monitors the wallet. Once user has authenticated using his fingerprint, encryption key is unlocked and wallet data is decrypted. The spyware instruments the app to retrieve this encryption key. It then exfiltrate the key and the wallet data to a remote server:
[سرایت مواد]

نتیجہ
As a conclusion, software wallets have different levels of security. However, their threat model does not cover the case of a malware running on the OS with a privilege escalation. This is by design: the wallet app cannot be more secure than the operating system it runs on.
- The isolation mechanism between apps provided by iOS/Android raises the bar for security compared to a software wallet running on a computer. The attacker needs first a privilege escalation to access app data.
- Key protection services (KeyStore, KeyChain) could add an additional layer of security for protecting secrets at rest. Nevertheless, as they don’t support cryptographic algorithms for cryptocurrency applications, keys have to be manipulated directly from the app, so they offer a limited protection.
- In all cases, an attacker with a root access, can either retrieve the seed at rest, when used, or leverage the user’s rights to empty the wallet using the software wallet as an oracle.


- SEO سے چلنے والا مواد اور PR کی تقسیم۔ آج ہی بڑھا دیں۔
- پلیٹوآئ اسٹریم۔ ویب 3 ڈیٹا انٹیلی جنس۔ علم میں اضافہ۔ یہاں تک رسائی حاصل کریں۔
- ایڈریین ایشلے کے ساتھ مستقبل کا نقشہ بنانا۔ یہاں تک رسائی حاصل کریں۔
- PREIPO® کے ساتھ PRE-IPO کمپنیوں میں حصص خریدیں اور بیچیں۔ یہاں تک رسائی حاصل کریں۔
- ماخذ: https://www.ledger.com/blog/software-wallets
- : ہے
- : ہے
- : نہیں
- :کہاں
- $UP
- 000
- 12
- 13
- 17
- 2020
- 24
- 27
- 39
- 500
- a
- کی صلاحیت
- قابلیت
- ہمارے بارے میں
- اوپر
- تک رسائی حاصل
- قابل رسائی
- اعمال
- سرگرمی
- اصل میں
- منسلک
- شامل کریں
- ایڈیشنل
- پتے
- انتظامیہ
- کے خلاف
- پہلے
- مقصد ہے
- یلگوردمز
- تمام
- کی اجازت
- اجازت دے رہا ہے
- کی اجازت دیتا ہے
- اکیلے
- ساتھ
- بھی
- ہمیشہ
- مقدار
- an
- اور
- لوڈ، اتارنا Android
- ایک اور
- جواب
- کوئی بھی
- اپلی کیشن
- درخواست
- ایپلی کیشنز
- ایپس
- کیا
- ارد گرد
- مضمون
- AS
- اثاثے
- ایسوسی ایٹ
- At
- حملہ
- حملے
- تصدیق شدہ
- کی توثیق
- واپس
- پچھلے دروازے
- حمایت کی
- بیک اپ
- بار
- کی بنیاد پر
- بنیادی
- BE
- بن
- رہا
- بیئر
- پیچھے
- کے درمیان
- اربوں
- بٹ کوائن
- بٹ کوائن کور
- کالی ٹوپی
- blockchain
- Blockchain.com
- بلوٹوت
- توڑ
- بروکرز
- جسمانی طاقت
- لیکن
- by
- کہا جاتا ہے
- کالز
- کیمرہ
- مہمات
- کر سکتے ہیں
- نہیں کر سکتے ہیں
- قبضہ
- کیس
- مقدمات
- چین
- سستے
- چیک
- میں سے انتخاب کریں
- منتخب کیا
- کلاس
- کوڈ
- Coinbase کے
- سکےباس والٹ
- COM
- کامن
- عام طور پر
- ابلاغ
- مواصلات
- مقابلے میں
- ہم آہنگ
- پیچیدہ
- کمپیوٹر
- کمپیوٹر
- نتیجہ اخذ
- اختتام
- حالات
- ترتیب
- کی توثیق
- سمجھا
- کنٹینر
- مواد
- کنٹرول
- کنٹرول
- مکالمات
- کور
- سکتا ہے
- جوڑے
- کورس
- احاطہ
- تخلیق
- مخلوق
- مجرم
- کرپٹو
- کرپٹو پرس
- کرپٹو کرنسیوں کی تجارت کرنا اب بھی ممکن ہے
- cryptocurrency
- کریپٹوکرنسی ایکسچینج
- cryptographic
- کرپٹپٹ
- وکر
- اعداد و شمار
- ڈیٹا کے تحفظ
- دسمبر
- خرابی
- وقف
- پہلے سے طے شدہ
- کی وضاحت
- منحصر ہے
- انحصار کرتا ہے
- اخذ کردہ
- تفصیل
- ڈیزائن
- ڈیزائن
- ڈیسک ٹاپ
- تفصیلی
- ترقی یافتہ
- آلہ
- کے الات
- DID
- اختلافات
- مختلف
- مشکل
- ڈیجیٹل
- ڈیجیٹل اثاثے۔
- براہ راست
- بات چیت
- دکھائیں
- ممتاز
- do
- کرتا
- نہیں
- نالی
- کافی
- کے دوران
- ہر ایک
- آسان
- آسانی سے
- ہنر
- یا تو
- الیکٹرم
- عنصر
- بیضوی
- یمبیڈ
- ایمبیڈڈ
- خفیہ کردہ
- خفیہ کاری
- توانائی
- انجنیئرنگ
- کافی
- درج
- داخل ہوا
- اندر
- ماحولیات
- اضافہ
- وغیرہ
- ethereum
- بھی
- مثال کے طور پر
- مثال کے طور پر
- اس کے علاوہ
- ایکسچینج
- پھانسی
- وجود
- خروج
- وضاحت کی
- بیان کرتا ہے
- دھماکہ
- استحصال کیا۔
- استحصال
- نکالنے
- حقیقت یہ ہے
- جعلی
- ممکن
- خصوصیات
- فائل
- فائلوں
- مل
- پتہ ہے
- فنگر پرنٹ
- پہلا
- کے بعد
- کے لئے
- مجبور
- سے
- پورا کریں
- تقریب
- فنڈز
- مزید برآں
- مستقبل
- حاصل کرنا
- عام طور پر
- پیدا
- پیدا
- پیدا ہوتا ہے
- پیدا کرنے والے
- حاصل
- دی
- اچھا
- گروپ
- اس بات کی ضمانت
- ہارڈ
- ہارڈ ویئر
- ہارڈ ویئر ڈیوائس
- ہارڈ ویئر والٹ
- ہارڈ ویئر والیٹ
- ہے
- he
- لہذا
- یہاں
- ان
- کس طرح
- تاہم
- HTML
- HTTPS
- خیال
- شناخت
- if
- پر عملدرآمد
- عمل
- متاثر کن
- in
- سمیت
- آزاد
- معلومات
- ابتدائی طور پر
- انسٹال
- مثال کے طور پر
- آلہ
- آلات
- ارادہ
- بات چیت
- انٹرایکٹو
- انٹرفیس
- میں
- سرمایہ کاری
- iOS
- تنہائی
- IT
- میں
- خود
- جون
- صرف
- رکھیں
- کلیدی
- چابیاں
- جان
- علم
- جانا جاتا ہے
- آخری
- پرت
- لیجر
- لیجر نانو
- کم
- سطح
- لیوریج
- ہلکا پھلکا
- LIMIT
- لمیٹڈ
- لینکس
- مقامی
- لو
- MacOS کے
- مین
- بنیادی طور پر
- مین سٹریم میں
- بنانا
- میلویئر
- مینیجر
- انتظام کرتا ہے
- لازمی
- جوڑی
- دستی
- بہت سے
- بہت سے لوگ
- ماسٹر
- مواد
- مواد
- زیادہ سے زیادہ چوڑائی
- کا مطلب ہے کہ
- میکانزم
- نظام
- درمیانہ
- یاد داشت
- میٹا ماسک
- طریقہ
- طریقوں
- منتقل
- میمونکس
- موبائل
- موبائل آلات
- ڈاؤن لوڈ، اتارنا
- ماڈل
- ماڈل
- مونیرو
- قیمت
- کی نگرانی
- نظر رکھتا ہے
- ماہ
- زیادہ
- اس کے علاوہ
- سب سے زیادہ
- زیادہ تر
- بہت
- ضروری
- نینو
- ضروری
- ضروریات
- کبھی نہیں
- پھر بھی
- نئی
- خبر
- نیسٹ
- نہیں
- خاص طور پر
- این ایس او گروپ
- تعداد
- حاصل کی
- حاصل
- of
- پیش کرتے ہیں
- کی پیشکش کی
- تجویز
- آف لائن
- اکثر
- on
- ایک بار
- والوں
- صرف
- کھولتا ہے
- کام
- آپریٹنگ سسٹم
- آپریٹنگ سسٹم
- or
- اوریکل
- OS
- دیگر
- پیداوار
- خود
- خاص طور پر
- پاس ورڈ
- پاس ورڈ مینیجر
- پاس ورڈز
- Pegasus کے
- لوگ
- کارکردگی
- کارکردگی کا مظاہرہ
- ذاتی
- فون
- فون کالز
- فونز
- جسمانی
- سادہ متن
- پلاٹا
- افلاطون ڈیٹا انٹیلی جنس
- پلیٹو ڈیٹا
- پوائنٹ
- نقطہ نظر
- مقبول
- ممکن
- پریکٹس
- پیشن گوئی
- پیش قیاسی
- پیش
- موجودہ
- اصولوں پر
- نجی
- نجی چابیاں
- استحقاق
- استحقاق
- عمل
- عمل
- پروگرام
- مناسب طریقے سے
- حفاظت
- محفوظ
- حفاظت
- تحفظ
- فراہم
- فراہم
- مقاصد
- QR کوڈ
- اٹھاتا ہے
- تصادفی پیدا
- رینج
- پڑھیں
- ریڈی میڈ
- اصلی
- اصلی رقم
- وجہ
- وجوہات
- حال ہی میں
- کم
- کے بارے میں
- باقاعدہ
- نسبتا
- انحصار کرو
- ریموٹ
- وسائل
- باقی
- دوبارہ استعمال
- حقوق
- جڑ
- جڑ تک رسائی
- رن
- چل رہا ہے
- اسی
- سینڈ باکسز
- منظر نامے
- سکرین
- SD
- خفیہ
- محفوظ بنانے
- محفوظ طریقے سے
- سیکورٹی
- سیکیورٹی کے خطرات
- دیکھنا
- بیج
- بھیجنے
- بھیجتا ہے
- حساس
- بھیجا
- تسلسل
- سروسز
- کئی
- دکھائیں
- سے ظاہر ہوا
- سائن ان کریں
- اشارہ
- دستخط کی
- اسی طرح
- سادہ
- بعد
- ایک
- ہنر مند
- اسمارٹ فونز
- SMS
- So
- سماجی
- معاشرتی انجینرنگ
- سافٹ ویئر کی
- کچھ
- بہتر
- خصوصی
- مخصوص
- خاص طور پر
- خرچ
- سپائیویئر
- رہنا
- چراغ
- ابھی تک
- چوری
- ذخیرہ
- ذخیرہ
- ذخیرہ
- پردہ
- براہ راست
- تعلیم حاصل کی
- اس طرح
- کافی
- مختصر
- حمایت
- تائید
- سطح
- کے نظام
- سسٹمز
- ہدف
- ھدف بنائے گئے
- اہداف
- ٹیکنیکل
- تکنیک
- عارضی
- سے
- کہ
- ۔
- مستقبل
- دنیا
- ان
- ان
- تو
- وہاں.
- یہ
- وہ
- تیسری پارٹی
- اس
- اگرچہ؟
- ہزاروں
- خطرہ
- خطرات
- کے ذریعے
- ٹکر
- وقت
- کرنے کے لئے
- کے آلے
- اوزار
- کھلونا
- ٹرانزیکشن
- معاملات
- درخت
- قابل اعتماد
- دو
- قسم
- اقسام
- کے تحت
- بنیادی
- بدقسمتی سے
- انلاک
- بے نقاب
- اپ ڈیٹ کرنے کے لئے
- USB
- استعمال کی شرائط
- استعمال کیا جاتا ہے
- رکن کا
- صارفین
- کا استعمال کرتے ہوئے
- عام طور پر
- تصدیق کریں۔
- قیمت
- اقدار
- اس بات کی تصدیق
- بہت
- وکٹم
- ویڈیو
- لنک
- نقصان دہ
- خطرے کا سامنا
- بٹوے
- بٹوے
- چاہتے ہیں
- چاہتا ہے
- تھا
- راستہ..
- we
- ویب
- مہینے
- تھے
- WhatsApp کے
- جب
- جس
- پوری
- وسیع
- وسیع رینج
- بڑے پیمانے پر
- وکیپیڈیا
- گے
- کھڑکیاں
- ساتھ
- الفاظ
- دنیا
- گا
- ابھی
- آپ
- اور
- یو ٹیوب پر
- زیفیرنیٹ